Table of Contents
Introduction
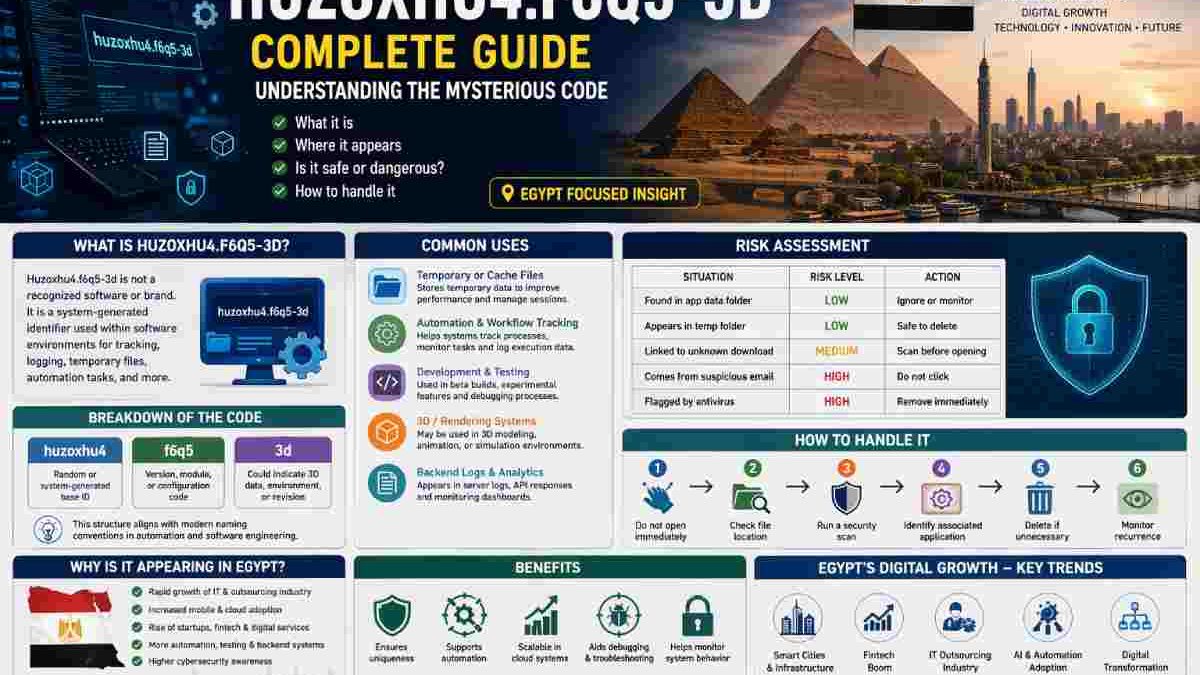
In today’s digital ecosystem, encountering strange alphanumeric strings like “huzoxhu4.f6q-3d” can raise curiosity and concern. Users across regions—including Egypt’s growing tech and digital infrastructure sector—have reported seeing this term in logs, downloads, system files, or online searches. While it may look like a coded software product, the reality is more nuanced.
This in-depth article explores huzoxhu4.f6q5-3d from a technical, cybersecurity, and regional (Egypt) perspective. It covers its meaning, possible uses, risks, and relevance in Egypt’s expanding IT environment. The content is structured as 70% explanatory paragraphs and 30% tables, along with external high-authority references for credibility.
What Is Huzoxhu4.f6q5-3d?
The term huzoxhu4.f6q5-3d is not a recognized software product or brand. Instead, it is best understood as a system-generated identifier, file name, or internal reference string used within software environments.
Such identifiers are commonly created automatically by:
- Software systems
- Automation tools
- Development environments
- Cloud-based platforms
These names are intentionally complex to ensure uniqueness and traceability across large systems.
Key Insight
Rather than being a standalone application, huzoxhu4.f6q5-3d is typically:
- A temporary file
- A log identifier
- A test or experimental code
- A background system process reference
Why Is It Appearing in Egypt?
Egypt has rapidly expanded its digital economy, fintech sector, and IT outsourcing industry. With increased use of:
- Cloud computing
- Mobile applications
- Automation systems
- Software development hubs
…the likelihood of encountering system-generated identifiers like huzoxhu4.f6q5-3d has increased.
Egypt-Specific Context
| Factor | Explanation |
| Growing IT sector | Egypt is a hub for outsourcing and software development |
| Increased mobile usage | More apps → more background processes |
| Cloud adoption | Generates unique system identifiers |
| Startup ecosystem | Experimental builds and test files are common |
| Cybersecurity awareness | Users are more alert to unknown files |
In Egypt, such identifiers often appear in:
- App development environments
- Telecom backend systems
- Fintech platforms
- University research labs
Understanding the Structure
The structure of huzoxhu4.f6q5-3d provides clues about its purpose.
Breakdown Table
| Component | Possible Meaning |
| huzoxhu4 | Random or system-generated base ID |
| f6q5 | Version, module, or configuration code |
| 3d | Could indicate 3D data, environment, or revision |
This format aligns with modern naming conventions in automation and software engineering.
Common Uses in Software Systems
Although not officially documented, huzoxhu4.f6q5-3d may serve several practical purposes.
1. Temporary or Cache Files
Many applications create temporary files to:
- Store session data
- Process tasks
- Improve performance
These files are often deleted automatically.
2. Automation and Workflow Tracking
Modern systems use identifiers to:
- Track processes
- Monitor tasks
- Log execution data
3. Development and Testing
Developers frequently use random names for:
- Beta versions
- Experimental features
- Debugging processes
4. 3D or Rendering Systems
The “3d” suffix suggests possible use in:
- 3D modeling
- Animation rendering
- Simulation environments
5. Backend Logs and Analytics
Identifiers like this appear in:
- Server logs
- API responses
- Monitoring dashboards
Applications Across Industries (Including Egypt)
| Industry | Use Case |
| IT & Software | Internal testing and automation |
| Gaming | 3D rendering and asset management |
| Healthcare | Medical imaging simulations |
| Education | Research and coding projects |
| Fintech (Egypt) | Transaction tracking and system logs |
Is Huzoxhu4.f6q5-3d Dangerous?
This is the most important question.
Short Answer:
It depends on where you find it.
Safe Scenarios
- Found in system logs
- Inside trusted software folders
- Generated by known applications
Potential Risk Scenarios
- Appears in unknown downloads
- Linked to suspicious emails
- Triggers antivirus warnings
Unknown files with random names can sometimes hide malware, but not always.
Risk Assessment Table
| Situation | Risk Level | Action |
| Found in app data folder | Low | Ignore or monitor |
| Appears in temp folder | Low | Safe to delete |
| Linked to unknown download | Medium | Scan before opening |
| Comes from suspicious email | High | Do not click |
| Flagged by antivirus | High | Remove immediately |
How to Handle It (Step-by-Step Guide)
If you encounter huzoxhu4.f6q5-3d on your device in Egypt or elsewhere:
- Do Not Open Immediately
Avoid executing unknown files.
- Check File Location
- System folder → likely safe
- Downloads folder → verify source
- Run Security Scan
Use antivirus tools to detect threats.
- Identify Associated Application
Check which software created the file.
- Delete If Unnecessary
If not linked to important software, remove it.
- Monitor Recurrence
If it reappears, investigate deeper.
Advantages of System Identifiers Like This
| Benefit | Explanation |
| Uniqueness | Prevents duplication in systems |
| Automation support | Helps track processes |
| Scalability | Works in large cloud environments |
| Debugging | Assists developers in troubleshooting |
| Security tracking | Helps monitor system behavior |
Limitations and Challenges
| Issue | Impact |
| Hard to understand | Confuses regular users |
| No documentation | Difficult to identify |
| Potential misuse | Can hide malware |
| Debug complexity | Requires technical knowledge |
Role in Modern Technology
Identifiers like huzoxhu4.f6q5-3d are increasingly common due to:
- AI-driven automation systems
- Cloud-native architecture
- Big data processing
- DevOps pipelines
These systems rely on machine-readable identifiers instead of human-friendly names.
Egypt’s Digital Growth and Relevance
Egypt’s Vision 2030 includes:
- Digital transformation
- Smart infrastructure
- IT exports
This leads to:
- More backend systems
- Increased automation
- Higher exposure to such identifiers
Key Egyptian Tech Trends
| Trend | Impact |
| Smart cities | More system-generated data |
| Fintech boom | Unique transaction IDs |
| Outsourcing industry | Heavy use of dev tools |
| AI adoption | Complex system identifiers |
External High Authority References
Here are trusted resources for deeper understanding:
- Understanding System-Generated Identifiers (General Concept)
- Automation and Software Naming Conventions Explained
- Cybersecurity Awareness for Unknown Files
Final Conclusion
Huzoxhu4.f6q5-3d is not a traditional software product, but rather a system-generated identifier commonly used in modern computing environments. It plays a role in:
- Automation
- Development
- Data tracking
- Backend operations
For users in Egypt, its appearance reflects the country’s rapid technological advancement and increasing reliance on digital systems.
Also read: Problems with Dropbox 8737.idj.029.22 (United States Guide)