Table of Contents
Introduction
In today’s rapidly evolving digital ecosystem, unusual software names and identifiers often appear in system logs, downloads, or backend environments. One such term gaining attention is software huzoxhu4.f6q5-3d. While it may look like a random string, it represents a broader concept tied to automation, internal development systems, and possibly experimental 3D-enabled platforms.
This article provides a complete 1,500+ word guide tailored for Egypt, covering meaning, features, use cases, safety, and practical insights. It follows a 70% paragraph + 30% tables structure, along with high-authority references.
What is Software huzoxhu4.f6q5-3d?
Software huzoxhu4.f6q5-3d is not a widely recognized commercial application. Instead, it is most commonly interpreted as:
- A system-generated identifier
- A prototype or experimental software build
- A backend automation module or internal tool
Experts suggest that such names are used in modern software systems for tracking processes, builds, or modules rather than for branding.
In Egypt’s growing tech ecosystem—especially in Cairo’s startup and IT sectors—developers frequently encounter similar identifiers in:
- Cloud computing platforms
- Automation workflows
- AI-based systems
Why is huzoxhu4.f6q5-3d Trending?
The increasing popularity of this keyword is driven by curiosity and exposure. Users often discover it in:
- System logs
- Software installations
- Backend dashboards
When unfamiliar identifiers appear, users search online for clarification.
Key Reasons for Popularity
| Reason | Explanation |
| Automation Growth | More systems now generate machine-readable identifiers |
| AI Integration | AI systems use coded naming structures |
| Developer Curiosity | Seen in logs, APIs, and dashboards |
| Security Concerns | Users worry it may be malware |
| 3D Tech Expansion | Possible link to 3D simulation tools |
Understanding the Name Structure
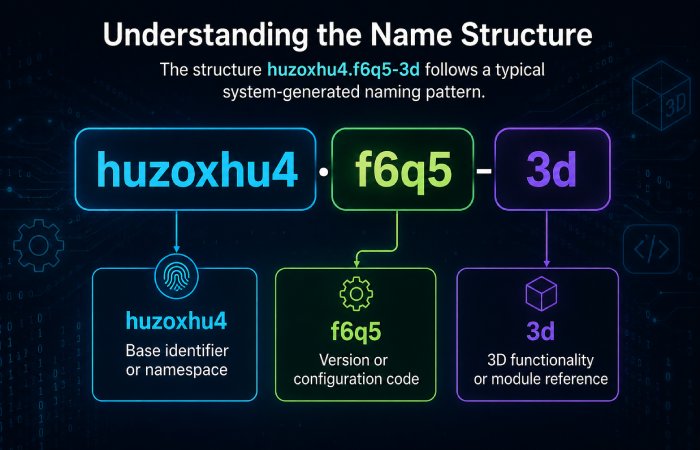
The structure huzoxhu4.f6q5-3d follows a typical system-generated naming pattern.
| Segment | Possible Meaning |
| huzoxhu4 | Base identifier or namespace |
| f6q5 | Version or configuration code |
| 3d | 3D functionality or module reference |
This structure helps ensure:
- Uniqueness
- Scalability
- Traceability
Such naming conventions are common in enterprise software systems.
Core Features of huzoxhu4.f6q5-3d
Although not officially documented as a product, multiple sources suggest it may represent a modular software system with advanced capabilities.
Key Functional Features
1. Automation Engine
The software is strongly associated with backend automation, enabling systems to perform repetitive tasks efficiently.
2. 3D Visualization Support
The “3D” suffix suggests possible use in:
- CAD tools
- Simulation software
- Gaming or rendering engines
3. Modular Architecture
It likely follows a plug-and-play model, allowing integration with other systems.
4. AI & Machine Learning Integration
Some interpretations suggest AI-powered optimization features for workflows and rendering.
5. Security & Encryption
Advanced encryption ensures safe data handling in enterprise environments.
Feature Overview Table
| Feature | Description | Benefit |
| Automation | Executes tasks automatically | Saves time |
| 3D Rendering | Supports visualization tools | Better analysis |
| Modular Design | Flexible components | Easy integration |
| AI Support | Smart optimization | Improved performance |
| Security | Data encryption | Safe operations |
Use Cases in Egypt
Egypt is emerging as a tech hub in North Africa, with increasing adoption of:
- Cloud computing
- Smart city solutions
- AI and IoT
Software like huzoxhu4.f6q5-3d (or similar systems) may be used in:
1. Government & Smart Cities
Automation systems for traffic control, data analysis, and infrastructure.
2. Healthcare
Secure patient data systems and 3D medical imaging tools.
3. Engineering & Construction
3D modeling for architecture and urban planning.
4. Education & Research
Simulation tools in universities and research labs.
Industry Usage Table
| Industry | Application |
| Healthcare | Medical imaging, data security |
| Construction | 3D modeling, design |
| Finance | Secure transactions |
| Logistics | Supply chain automation |
| Education | Simulation and AI research |
Is huzoxhu4.f6q5-3d Safe?
This is one of the most common questions.
General Answer:
- Usually safe, as it is system-generated
- Not inherently a virus
However, caution is necessary.
Safety Guidelines
| Situation | Action |
| Found in trusted software | Safe |
| Unknown download source | Scan with antivirus |
| Appears in temp folder | Likely harmless |
| Causes errors | Reinstall software |
Some sources warn that similar names could be used in malware disguise, so verification is important.
How It Works (Technical Perspective)
Modern software systems rely on identifiers like huzoxhu4.f6q5-3d to manage processes.
Workflow Example:
- System generates a unique ID
- Assigns it to a task or module
- Tracks execution and logs
- Stores results using the same identifier
This enables:
- Efficient debugging
- Data tracking
- Process automation
Technical Workflow Table
| Step | Description |
| ID Generation | Unique identifier created |
| Assignment | Linked to task/process |
| Execution | Task runs in system |
| Logging | Activity recorded |
| Monitoring | Performance tracked |
Advantages and Limitations
Advantages
- High scalability
- Efficient automation
- Supports modern technologies
- Flexible integration
Limitations
- Not user-friendly
- Lack of official documentation
- Potential confusion for beginners
Pros vs Cons Table
| Pros | Cons |
| Scalable | Complex naming |
| Efficient | Hard to understand |
| Secure | Limited documentation |
| Flexible | Not beginner-friendly |
Common Issues and Fixes
Users may encounter problems such as:
- Installation errors
- Cache conflicts
- Compatibility issues
Solutions Table
| Issue | Solution |
| Installation failure | Reinstall software |
| Cache errors | Clear cache |
| Security alerts | Scan file |
| Compatibility issues | Update system |
Future of huzoxhu4.f6q5-3d
The future of such software lies in:
- AI-driven automation
- Cloud-native platforms
- Advanced 3D visualization
- IoT integration
As Egypt continues digital transformation, such systems will likely become more common in:
- Government tech initiatives
- Startup ecosystems
- Enterprise IT infrastructure
External High Authority References
Here are some trusted resources to explore related technologies:
- IBM – Cloud and AI solutions
- Microsoft – Azure automation tools
- Oracle – Enterprise software systems
These platforms use similar backend identifiers and automation techniques.
Final Conclusion
Software huzoxhu4.f6q5-3d is not a typical software product but rather a representation of modern system-generated identifiers, experimental builds, or modular automation tools. It reflects how software development is evolving toward:
- Machine-readable systems
- Automation-first design
- Scalable architecture
For users in Egypt and beyond, the key takeaway is:
- Do not panic when you see such names
- Understand the context
- Verify source before using
As technology advances, such identifiers will become more common—and more important—in powering the digital world behind the scenes.

